-
Our offeringsDigital Risk ProtectionEmergency Response ServicesCyber Threat IntelligenceSpecialized ServicesFeatured News

Our Latest Threat Matrix Report Is Out! Where we break down the latest threat developments and share what organisations should be preparing for in 2026.
- Your challenges
- Resources
-
About us
- Cyberhagen
- Careers
-
-
Digital Risk Protection
-
Emergency Response Services
-
Cyber Threat Intelligence
-
Specialized Services
-
About us
THREAT CLOUD

Relevant actionable valuable
As a cybersecurity professional, you know that information about cyber security threats that are external to your organization is critical.
The threat of malware attacks is basically an arms race between the security industry and the threat actors responsible for cyber-crime, where the latter are constantly looking for ways to circumvent existing defenses. Having access to indicators of compromise from the latest malware campaigns is an important tool in the efforts to mitigate this threat.

Strategic and operational CTI
The Threat Cloud service delivers powerful strategic and operational threat intelligence, enabling your organization to gain a comprehensive understanding of threat actors and their infrastructure.
With access to an extensive investigation platform encompassing numerous threat actors and their connection to specific IOCs/IOAs, users can effectively delve into their attack patterns to strengthen their response strategies.
Use cases. Incident investigation.
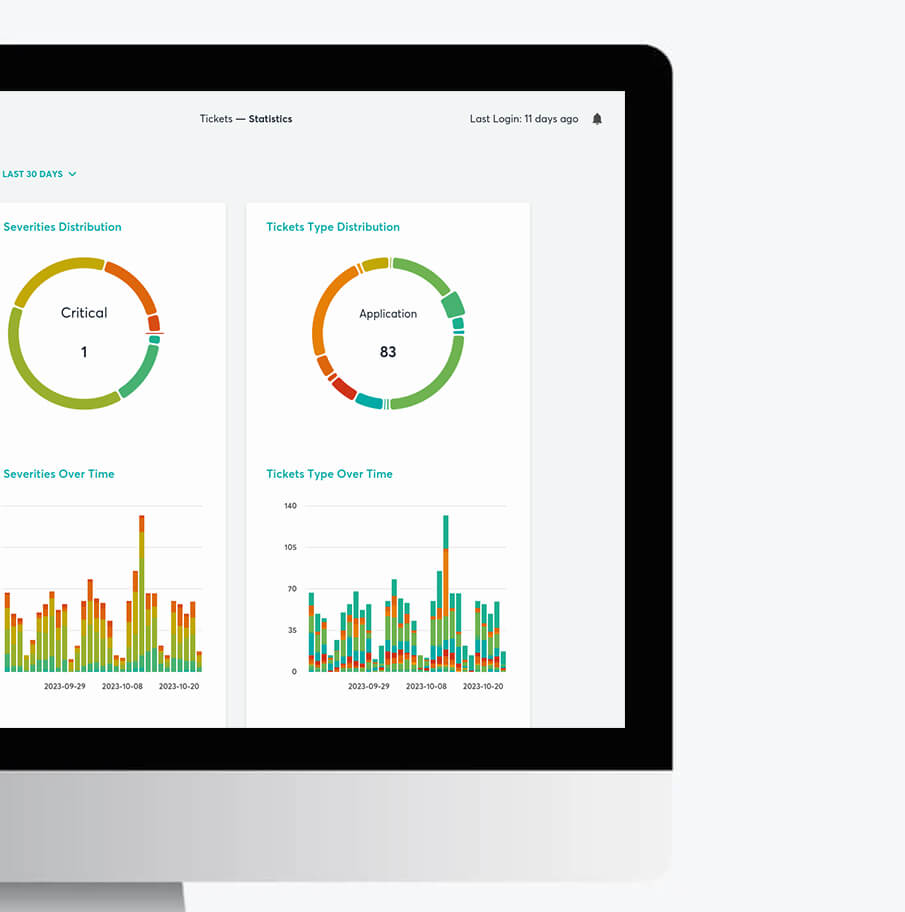
Our Threat Intelligence Portal
Threat Cloud aggregates the data our researchers routinely collect, the data our emergency responders gather during incident response work, and data from hundreds of private and public sources.
Threat Cloud is available via our cloud-based portal and provides the following capabilities:
- The ability to search for Indicators of Compromise: Domains, Hostnames, URLs, IP Addresses. Further contextual information is also provided, such as: Category, First Seen timestamps, C2 information, DNS and Nameserver records, as well as any additional historical info.
- Visualization of connections between items through graph functionality

CTI improves your cyber resilience
Threat Cloud allows users to search for information about files, URLs, IP addresses, domains, and more. It also provides detailed reports on threat types, threat actors, their tactics, techniques, and procedures (TTPs), and another relevant context.
Request a demo
Rest Assured.
We are the leader in actionable and intelligence-driven detection and response services.
